Cracking the Locker

During one of our red team engagements late last year, we were given a challenge:
Once inside the building, could we access employee lockers?
At first glance, this didn’t sound too exciting. But like many things in security, the small details often hide the biggest risks.
The Setup
From our reconnaissance, we discovered that the lockers were secured with Digilock Sola electronic locks - the kind often found in premium gyms, offices, and coworking spaces.
These weren’t your standard swimming-pool-style lockers with simple wafer locks you could jiggle open in seconds - these were smart locks secured with PINs and authorised electronic keys.

Access methods included:
- PIN codes: Users can enter a numeric code on the keypad. This is the most common setup for shared lockers because it’s easy to manage and doesn’t require issuing hardware.
- Electronic keys: Small physical devices that communicate with the lock. They can act as personal keys, manager keys, or programming keys. These tend to be more expensive, so facilities that use shared lockers usually rely on PINs instead.

The system is designed so that individual users have their own PINs, while a manager or programming key can override and access all lockers. For our client, given the setup and shared use, it was likely that most users relied on PINs.
We decided to dig deeper, purchasing an identical lock online for analysis and lab testing.
A Clue from the Community
While preparing our tests, we came across an eye‑opening paper from DEFCON 32 titled “Open Sesame – How Vulnerable Is Your Stuff in Electronic Lockers?”, which detailed how Sola locks could potentially be attacked to extract credentials.
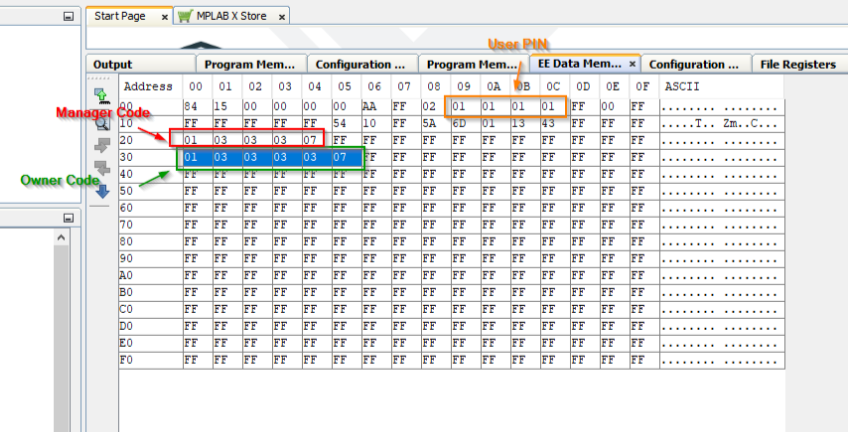
The research showed that physical access to an unlocked Sola lock could allow extraction of sensitive data, including manager credentials and user PINs, directly from the device’s internal memory.
This suggested that for certain models, an attacker might be able to access a user’s PIN or emulate a manager key capable of opening multiple lockers. That immediately got our attention.
Our Experiment
Lab Test
To see the research in action, we examined an identical lock in our lab, reproducing the method published in the DEFCON 32 paper. Our replication produced the same general results: structured credential data appeared in the lock’s internal memory.

Real-World Observation
Our testing was performed on a stand‑alone, unmanaged lock, while the locks on site were likely part of a managed system, meaning a single manager key could potentially unlock multiple lockers.
Although the technique worked in the lab, we weren’t permitted to disassemble or remove production locks during the engagement, so we couldn’t confirm whether those devices were affected in the same way.
Still, during our on‑site walkthrough we noticed multiple lockers left unlocked - exactly the condition an attacker would need to attempt this type of access.
So What?
While we didn’t confirm this on the production locks, our lab results combined with the unlocked lockers observed on site highlight a realistic risk scenario. In a managed system, a single compromised manager credential could, hypothetically, grant access to multiple lockers, putting personal items, sensitive documents, or other valuables at risk.
On top of that, users often reuse PINs across devices and accounts - for ATM cards, mobile phones, or computers. An attacker who extracts a locker PIN could potentially try the same code elsewhere, amplifying the impact beyond the lockers themselves.
Recommended Mitigations
To reduce risk, organisations using similar electronic lockers should:
- Confirm model details with the vendor to determine whether it is susceptible to credential extraction or emulation.
- Limit and monitor phyiscal access to locker areas.
- Consider upgrading older hardware to models with stronger protections.
- Educate users on proper locker hygiene - always lock after use, report malfunctions, and avoid reusing simple PINs.
Even small behavioural or procedural changes can make a meaningful difference in real-world resilience.
Closing Thoughts
This exercise highlighted how physical and digital systems intersect. Red teaming is not just about “breaking in”; it’s about identifying overlooked risks and helping organisations address them before they can be exploited.
Even minor elements, like lockers, can become meaningful points of exposure if not properly managed. The value lies in uncovering gaps, guiding practical mitigations, and strengthening overall security posture.
About SilentGrid
SilentGrid is a cybersecurity company specialising in red teaming, penetration testing, and security assessments. We help organisations uncover hidden risks across digital and physical environments and provide actionable guidance to strengthen their security posture. Learn more at silentgrid.com.




